Unlocking the Potential of XML in AI and Data Processing
Summarize with:
In an effort to optimize their digital processes and prepare for an AI-driven future, more publishers are now turning to XML file conversion to create structured, machine-readable content. Modern publication procedures increasingly rely on XML, especially those aiming to tap into the power of machine learning. By converting content into a standardized XML format, publishers can unlock new possibilities—automating content tagging, enabling hyper-personalized reader recommendations, and streamlining digital workflows for greater scalability and efficiency.
In this blog, we’ll explore the best practices for integrating XML content into machine-learning workflows explicitly tailored for publishers. With these strategies, you’ll be able to optimize your content handling while also enhancing efficiency and scalability in ways that push your publishing capabilities further than ever before.
Table of Contents:
- XML File Conversion, Explained!
- XML Content in the Context of Machine Learning Workflows
- Key Characteristics of XML
- Understanding the Vulnerabilities
- Building a Secure Fortress
- Best Practices for XML Content Integration in Machine Learning
- How XML Conversions Enhance Data Security?
- The Bottom Line
XML File Conversion, Explained!
XML, or Extensible Markup Language, is a versatile markup language specifically designed for data storage and seamless transfer across multiple platforms and applications.
XML file conversion refers to the data transformation process between XML and other file formats, such as Word, Excel, PDF, or image files. XML files are saved with the .xml extension and are a popular choice for representing arbitrary data structures in web services and building web-based applications.
XML Content in the Context of Machine Learning Workflows
Content in XML form is no longer just a data format for publishers. Publishers need an XML workflow because it’s essential for organizing and managing data. XML is perfect for integrating into machine learning workflows because it allows publishers to arrange content in a machine-readable and human-readable way.
Machine learning models can process, evaluate, and learn from content more quickly when formatted in XML, which eventually supports more accurate and efficient data-driven operations.
When content is structured in XML, machine learning models find it easier to process, analyze, and learn from. This ultimately supports more efficient and accurate data-driven publishing processes.
Key Characteristics of XML
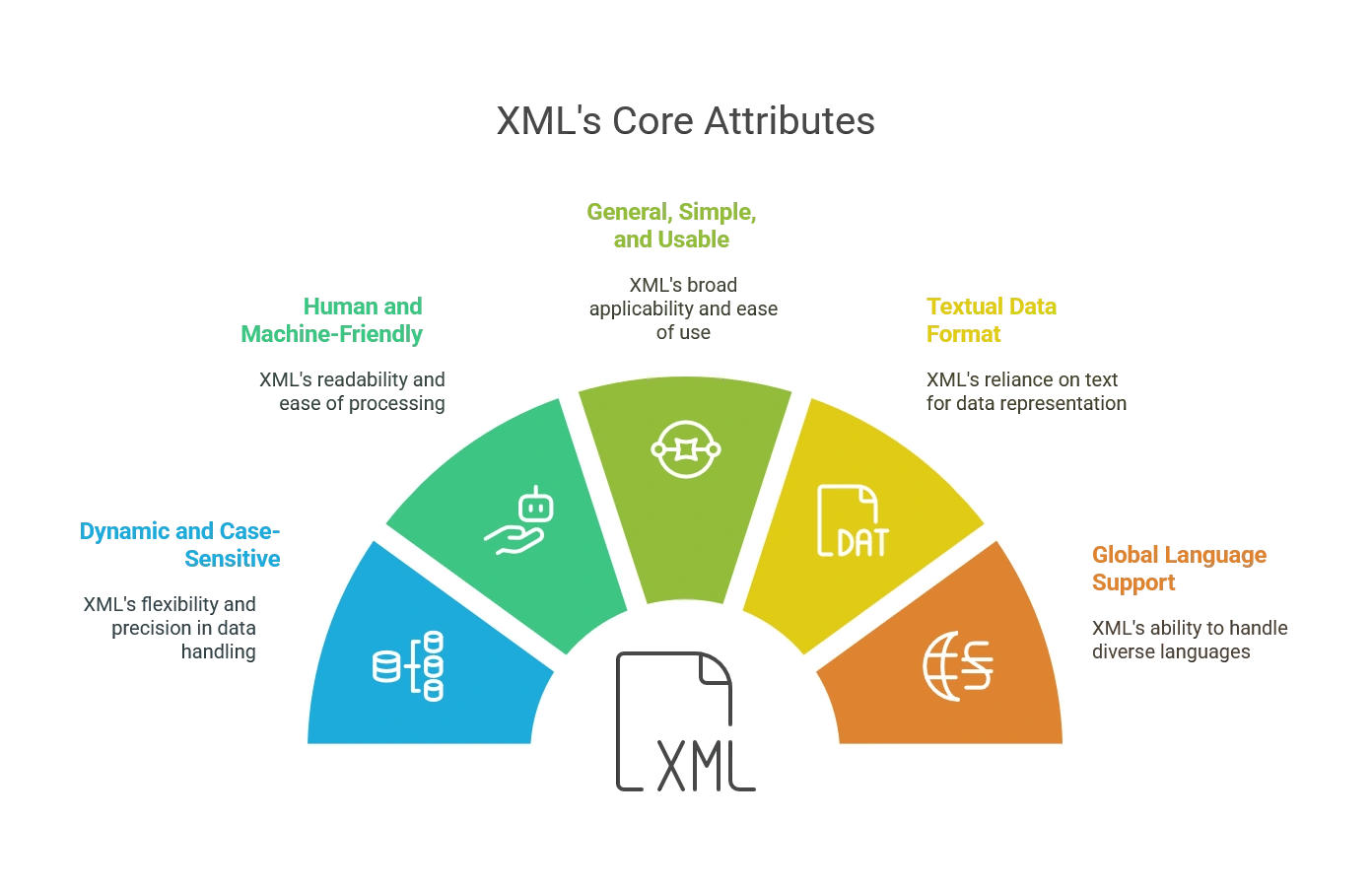
Here is a description of five key characteristics of XML:
1. Dynamic and Case-Sensitive
Unlike generic data formats, XML’s tags and attributes are self-defining and case-sensitive, ensuring precision and eliminating ambiguity. This meticulousness guarantees the accurate interpretation of data, preventing misinterpretations and data loss.
2. Human and Machine-Friendly
Striking a remarkable balance, XML is human-readable and easily parsed by computers. Its clear structure and hierarchical organization make it readily understandable for humans, while its tags and attributes provide machine-readable instructions for efficient processing.
This dual nature promotes collaboration and communication between humans and machines, optimizing data-handling workflows.
3. General, Simple, and Usable
Developed with widespread application in mind, XML boasts a straightforward design and broad compatibility. This makes it easily adaptable to various data types and readily deployable across diverse platforms and applications, empowering users to tailor XML to their needs.
4. Textual Data Format
Unlike proprietary formats, XML files are plain text documents with the .xml extension. It not only promotes accessibility and interoperability but also ensures long-term data preservation.
Unlike binary formats, plain text is platform-independent and resistant to obsolescence, guaranteeing that your data remains accessible and interpretable decades later.
5. Global Language Support
Recognizing the interconnectedness of our world, XML embraces Unicode, a universal character encoding standard. It empowers XML to represent text in diverse languages, facilitating seamless data exchange across geographical and cultural boundaries.
This multilingual capability makes XML an invaluable tool for fostering collaboration and understanding.
Understanding the Vulnerabilities
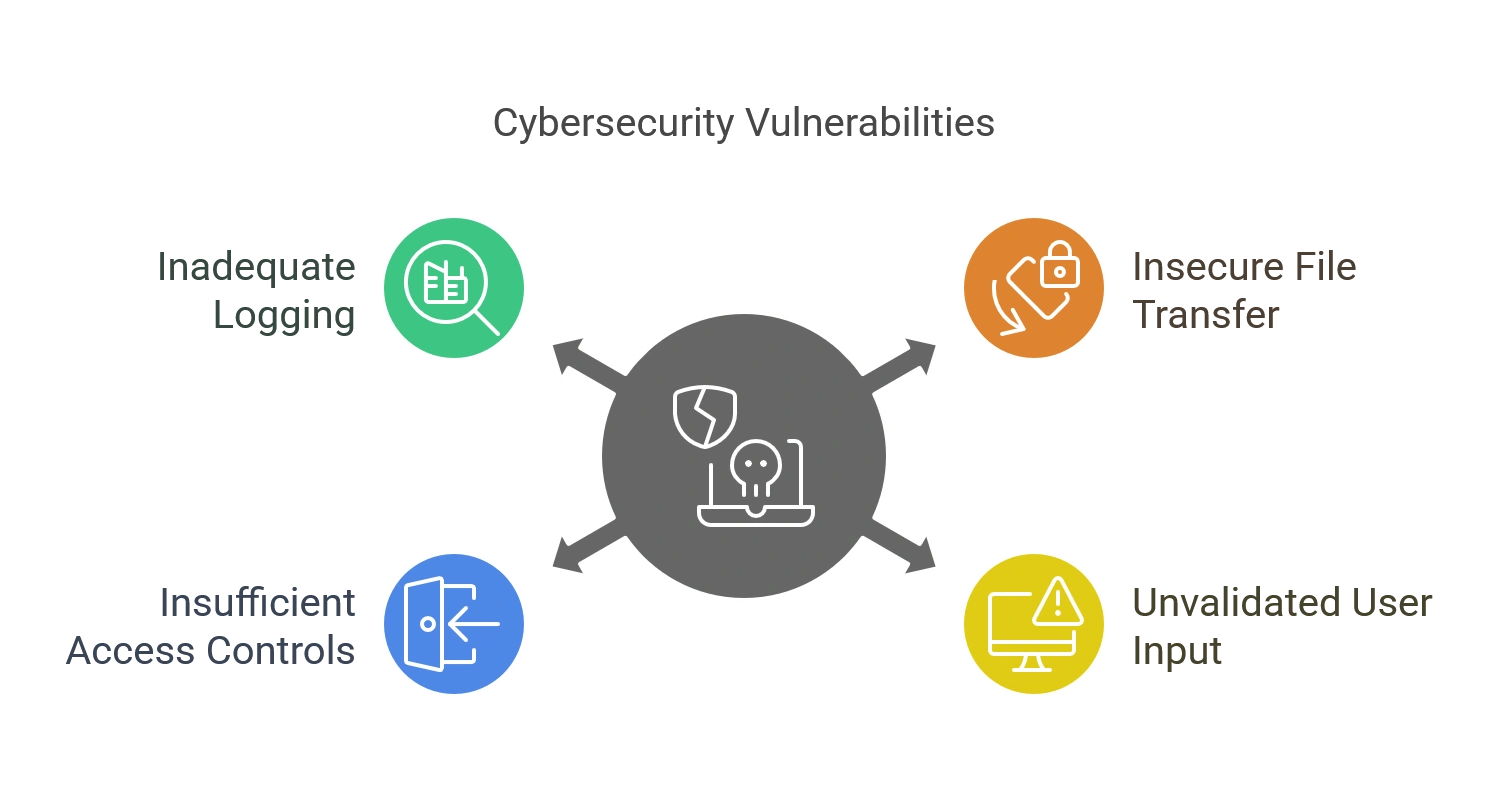
Before crafting countermeasures, it is vital to identify potential threats inherent in XML file conversion. These threats are:
1. Insecure File Transfer Protocols
Traditional methods like FTP rely on plaintext transmission, leaving data vulnerable to interception and manipulation. This lack of encryption creates a clear channel for malicious actors to steal sensitive information or inject unauthorized content.
2. Unvalidated User Input
Unchecked user input poses a significant risk, as malicious code or unauthorized access points can be disguised within seemingly legitimate data.
Failing to validate all user input exposes systems to vulnerabilities like SQL injection and cross-site scripting attacks, potentially compromising entire databases.
3. Insufficient Access Controls
Granular access control is crucial for safeguarding sensitive data. Without proper implementation, unauthorized individuals might gain access to confidential information, modify critical settings, or disrupt essential operations.
4. Inadequate Logging and Monitoring
A lack of comprehensive logging and monitoring hinders the ability to detect and investigate potential security incidents. Malicious actors can operate undetected when suspicious activity goes unnoticed, causing significant damage before their actions are identified.
Building a Secure Fortress
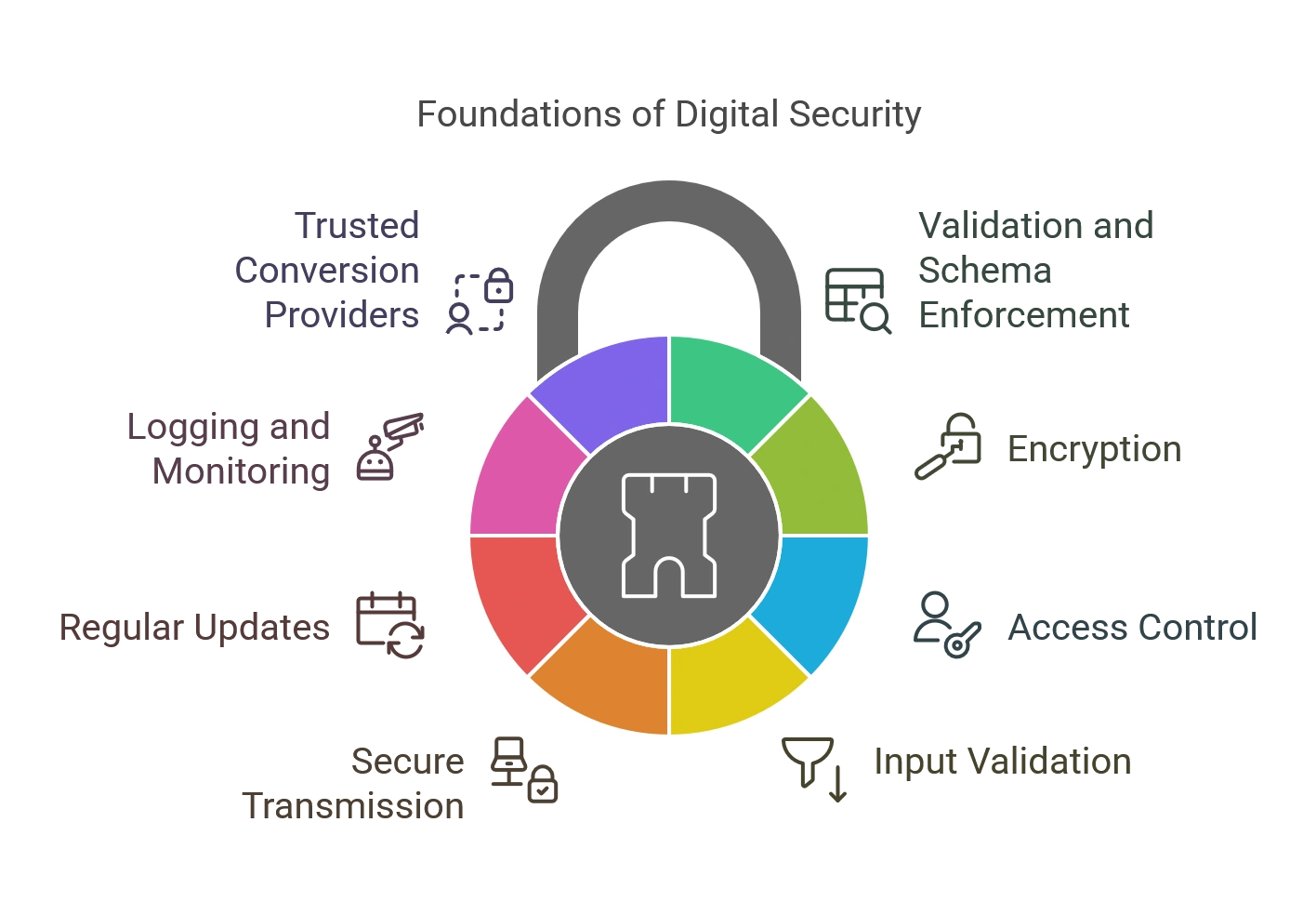
A layered security approach to XML conversion is essential to combat these threats. Here are key strategies to safeguard sensitive information:
1. Validation and Schema Enforcement
Embrace XML Schema Definition (XSD) to define data structure and constraints. Utilize XML validation tools to verify adherence to these rules, preventing malformed or malicious content infiltration.
2. Encryption
Lock up sensitive data within XML documents with encryption like AES or RSA.
These digital padlocks make information unreadable for unauthorized entities, ensuring confidentiality both in transit and storage. Enhance security further by using protocols like HTTPS and SFTP that encrypt data in transit, minimizing the risk of interception.
3. Access Control
Implement granular access control mechanisms based on user roles and permissions to restrict XML document usage to authorized users and processes. Define permissions based on roles and needs, minimizing exposure and potential misuse.
4. Input Validation
Sanitize and validate all external inputs before incorporation into XML publishing. Prevent injection attacks like XSS and XXE that exploit vulnerabilities to execute malicious code or access sensitive data.
5. Secure Transmission
Opt for HTTPS for encrypted data transfer over networks. Minimize interception and eavesdropping risks, safeguarding information confidentiality.
6. Regular Updates
Stay vigilant for vulnerability updates and promptly apply them to XML tools and libraries. Adopt industry best practices for secure XML handling.
These proven strategies provide invaluable guidance and minimize vulnerabilities in your systems. Ensure your applications and XML file conversion tools are always up-to-date to eliminate known weak points that attackers could use to infiltrate your systems.
7. Deploy Comprehensive Logging and Monitoring
Implementing comprehensive logging readily flags unusual access attempts, suspicious data alterations, or unauthorized modifications, enabling swift investigation and mitigation.
Reconstruct the timeline of events leading up to a potential security incident, pinpoint the source, and implement targeted corrective measures
8. Choose Trusted Conversion Providers
Outsourcing data conversions can streamline efficiency and expertise, allowing you to focus on core tasks while reliable experts handle your conversions.
When outsourcing conversions, opt for a reputable provider of data conversion services with a strong track record of data security and compliance with relevant regulations.
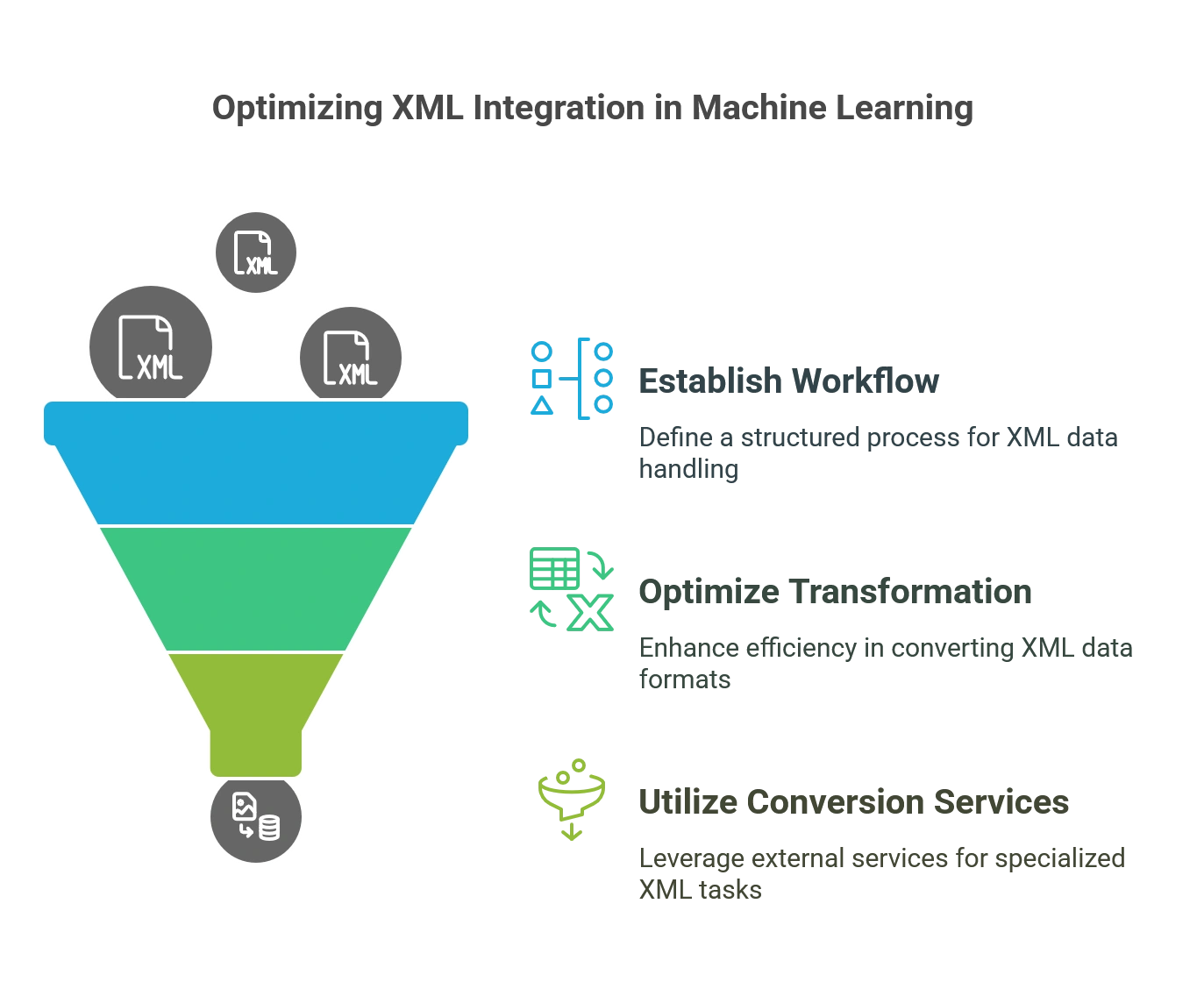
Best Practices for XML Content Integration in Machine Learning
Check out the key best practices that can help publishers seamlessly integrate XML content into machine learning processes, resulting in better data quality and performance.
1. Establish a Clear XML Workflow
A robust XML workflow is the foundation of any successful machine-learning project.
- The first step in setting up this workflow is to standardize XML content across your organization. Publishers often work with multiple content types, leading to inconsistent XML structures. To overcome this, develop a consistent scheme and metadata standards that all XML content must adhere to.
- Next, automate the XML content extraction process to avoid manual errors and speed up data processing. Use tools that support automated tagging and metadata extraction to streamline content preparation for machine-learning applications. Additionally, ensure that the XML content development includes all necessary metadata, such as content tags, categories, and timestamps, making the data more valuable when used in machine learning algorithms.
- Another key point is version control. Since XML content might vary over time, monitoring modifications made to various iterations is critical. When version control systems like Git are used, all stakeholders can work with the most recent XML files, and alterations are effectively controlled.
- Finally, data validation must be ensured during every step of the workflow. Implement validation checks to catch any discrepancies in the XML data before it enters the machine learning pipeline.
2. Optimize XML Transformation and Conversion Processes
One of the most significant advantages of XML content in machine learning is its flexibility, but this flexibility requires proper transformation and conversion. XML transformation allows you to adapt XML data for various machine learning tasks, such as content classification, sentiment analysis, recommendation engines, etc.
To optimize XML transformation, publishers should employ tools like XSLT to convert XML into different formats for machine learning models. For example, converting XML content into CSV formats can help machine learning platforms more easily ingest the data.
Another important aspect is data cleanliness. When transforming XML content, check that the data is free from inconsistencies, missing values, or duplicate entries.
For publishers handling large volumes of XML content, batch processing should be used to automate transformation and conversion. Set up automated pipelines that transform and convert XML data in batches, saving time and effort while maintaining high accuracy.
4. Utilize XML Conversion Services
Working with XML conversion services can be a game-changer in certain situations, particularly for advanced XML content integration. These services provide expert-level support for transforming XML content into different formats or integrating it more efficiently into machine-learning workflows.
When considering XML conversion services, choosing a provider with expertise in publishing-specific XML needs is crucial. Check for services like Hurix Digital that have experience handling content that follows specific XML publishing standards, such as those used for eBooks, academic articles, or multimedia content.
As your content library grows, scalability becomes essential. Opt for cloud-based XML conversion services that can handle large volumes of data with minimal slowdown. Finally, get detailed quotes and compare options to find a provider that balances affordability with quality.
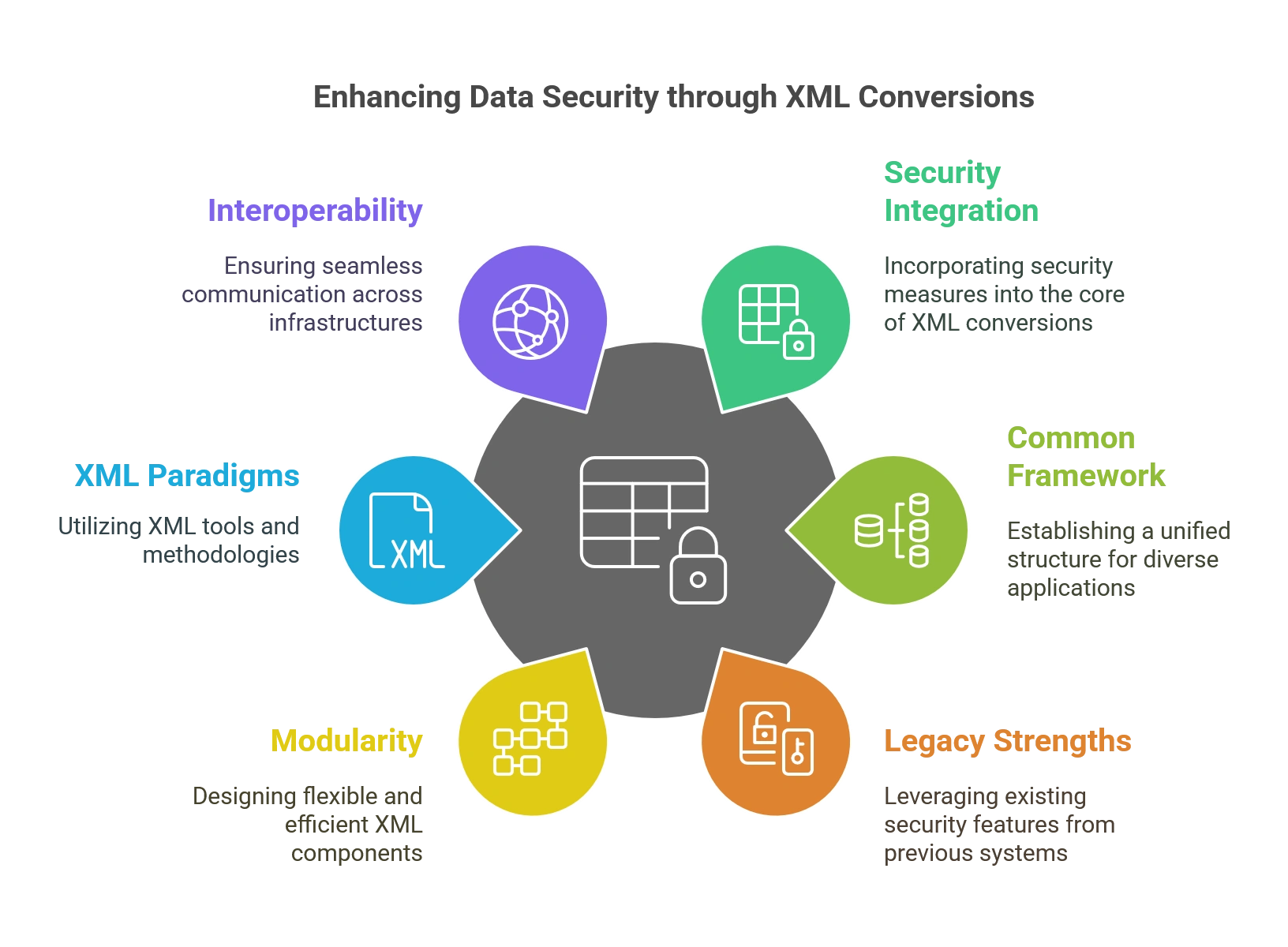
How XML Conversions Enhance Data Security?
While XML excels in data organization and exchange, its role in bolstering data security is equally significant.
Let’s see how XML File Conversion contributes to a secure information landscape:
1. Integration of Security into the Core
XML conversion seamlessly incorporates security measures into the XML structure, ensuring confidentiality, integrity, and authenticity without compromising the format’s versatility.
This fusion enables the application of security mechanisms to entire XML publishing documents or specific sections, preserving compatibility with standard XML tools.
2. Common Framework for Diverse Applications
Establish a standardized framework and processing rules, fostering interoperability across diverse applications and tools. It eliminates the need for extensive customization in each application to implement security, streamline adoption, and reduce overhead.
3. Inheritance of Legacy Security Strengths
XML file conversion stands on the shoulders of giants, incorporating proven concepts, algorithms, and technologies from established security systems. This inheritance ensures a solid foundation while tailoring these elements to align with XML’s unique structure and requirements.
4. Modularity for Flexibility and Efficiency
Ensure XML transformation embraces a modular approach, defining minimum mechanisms to achieve comprehensive security. It enables organizations to select and implement only the necessary components, optimizing resource allocation and reducing complexity.
5. Harnessing XML Paradigms and Tools
By aligning with XML’s design principles and leveraging existing XML tools, minimize the need for extensive application modifications. The smooth integration fosters adoption and simplifies security management within XML-centric environments.
6. Interoperability Across Infrastructures
XML file conversion promotes seamless interoperability with a broad spectrum of existing security infrastructures and deployments. This harmonization enables organizations to protect sensitive information as it flows across diverse systems and platforms.
While implementing robust security measures may require an initial investment, the long-term benefits far outweigh the costs. Data breaches can result in substantial financial losses, reputational damage, and legal repercussions.
By prioritizing data security in your XML file conversion processes, you protect valuable information, ensure compliance with regulations, and foster trust with your stakeholders.
Check out EXCLUSIVE: Hurix Digital Converts XML Files to HTML and Publishes 250,000 Backlist Titles
The Bottom Line
Data security is an ongoing endeavor, and enhancing security measures in XML file conversion processes requires a proactive and comprehensive approach. Embedding security measures within the XML structure itself ensures that XML security transcends traditional security boundaries.
The inherent integration safeguards data integrity, confidentiality, and authenticity while fostering seamless interoperability and simplified adoption. Establishing a secure foundation for data in the world of XML conversion is more than simply an option- it is a necessity.
Although online XML File conversion tools exist, internally managing large-scale conversions can be time-consuming and resource-intensive. Partnering with an experienced XML data conversion services provider like Hurix Digital ensures high degrees of accuracy in the conversion process, minimizing errors and data loss.
Our secure file transfer methods and encryption safeguards protect sensitive information throughout the conversion process. Multi-level quality checks ensure the integrity and consistency of converted data.
With our expertise, we help you unlock the true potential of XML for your publishing needs. Connect with us today!
Summarize with:

Vice President – Content Transformation at HurixDigital, based in Chennai. With nearly 20 years in digital content, he leads large-scale transformation and accessibility initiatives. A frequent presenter (e.g., London Book Fair 2025), Gokulnath drives AI-powered publishing solutions and inclusive content strategies for global clients
 A Space for Thoughtful
A Space for Thoughtful 




